Smart devices: using them safely in your home
<div>Many everyday items are now connected to the internet: we explain how to use them safely.</div>
<div>Many everyday items are now connected to the internet: we explain how to use them safely.</div>
<div>Risk appetites; what are they, what’s their purpose, how do organisations go about defining them?</div>
<div>Why I'm trying desperately to stop saying 'it depends' when it comes to simple cyber security questions...</div>
<div>The NCSC's Cloud Security Research Lead suggests some approaches to help you get confidence in cloud services.</div>
<div>An updated report from the NCSC explaining how UK law firms - of all sizes - can protect themselves from common cyber threats.</div>
<div>Recommended profiles to securely configure TLS for the most common versions and scenarios, with additional guidance for managing older versions.</div>
<div>How setting up 2SV can help protect your online accounts, even if your password is stolen.</div>

In the glamorous and historic heart of Monaco, the ABB FIA Formula E World Championship Monaco E-Prix unfolds, a spectacle that captivates the world. This event is more than just a race. It's a testament to the power of technology—specifically software—in shaping the future. The partnership between OpenText and Jaguar TCS Racing is a collaboration that embodies the fusion of historic elegance and modern speed, powered by the transformative capabilities of real-time data analytics. Historic t

<div>The watchdog wants to examine whether the deals fall within UK merger rules or raise competition concerns</div>
I built a beautiful teleprompter to sound more confident on cold calls or videos. Check it out https://magicscript.vercel.appI Recently had the experience of recording a quick demo for one of my products, and i was taking 3 second long pauses and blanking when the record button hit. I found that a lot of other teleprompters on the market were just too complex or had terrible UI/UX and didn't really allow navigation abilities.I recorded the demo video on my landing page using
Been looking for a job since December 2023-- for the 1st few months of 2024 there was maybe 1 job a month. (Edited to add: this was in January/Feb, when I was only seeing 1-2 job posts a month. I am seeing more now, but being ghosted, see below)A few more jobs now, but still havent had a single interview. I send my CV and it goes into some blackhole and I never hear anything back.I could understand if I was being rejected after interviews, but Im not even getting to that stage. My CV isn&#x

Malware Campaign Hijacks eScan Antivirus Updates for Backdoor and Cryptocurrency Miner Distribution Post Views: 2 (adsbygoogle = window.adsbygoogle || []).push({});
<div><h4>Why the triple threat of ransomware, data breaches, and extortion is a cybersecurity crisis</h4> <p>The UK government could be forgiven for wanting to forget March 2024 ever happened.…</p></div>
<div>Hackers have been using a sophisticated man-in-the-middle attack to exploit a vulnerability in an antivirus solution to spread backdoors on corporate networks</div>
<div>For large, complex firms struggling with the prescriptiveness of Cyber Essentials, ‘Pathways’ will provide a new route to certification.</div>
Attackers are employing evasion techniques to bypass detection and extend dwell time on compromised systems. This is achieved by targeting unmonitored devices, leveraging legitimate tools, and exploiting zero-day vulnerabilities. While defenders are improving detection speed (dwell time decreased from 16 to 10 days), this is partly due to faster ransomware identification and adversary-in-the-middle and social engineering tactics to bypass multi-factor authentication. Cloud infrastructure

<div>HPE’s new Wi-Fi access points add more capacity for wireless traffic and the option to process IoT data faster</div>
Google addressed a critical Chrome vulnerability, tracked as CVE-2024-4058, that resides in the ANGLE graphics layer engine. Google addressed four vulnerabilities in the Chrome web browser, including a critical vulnerability tracked as CVE-2024-4058. The vulnerability CVE-2024-4058 is a Type Confusion issue that resides in the ANGLE graphics layer engine. An attacker can exploit this vulnerability to execute arbitrary code on a victim’s machine. This critical flaw was reported by Toan
Cisco has released critical security updates to address multiple vulnerabilities in its Adaptive Security Appliance (ASA) devices and Firepower Threat Defense (FTD) software, collectively known as the “ArcaneDoor” vulnerabilities. If exploited, these vulnerabilities could allow a cyber threat actor to take control of an affected system. The Cybersecurity and Infrastructure Security Agency (CISA) has added two vulnerabilities to its Known Exploited Vulnerabilities Catalog, indicating acti
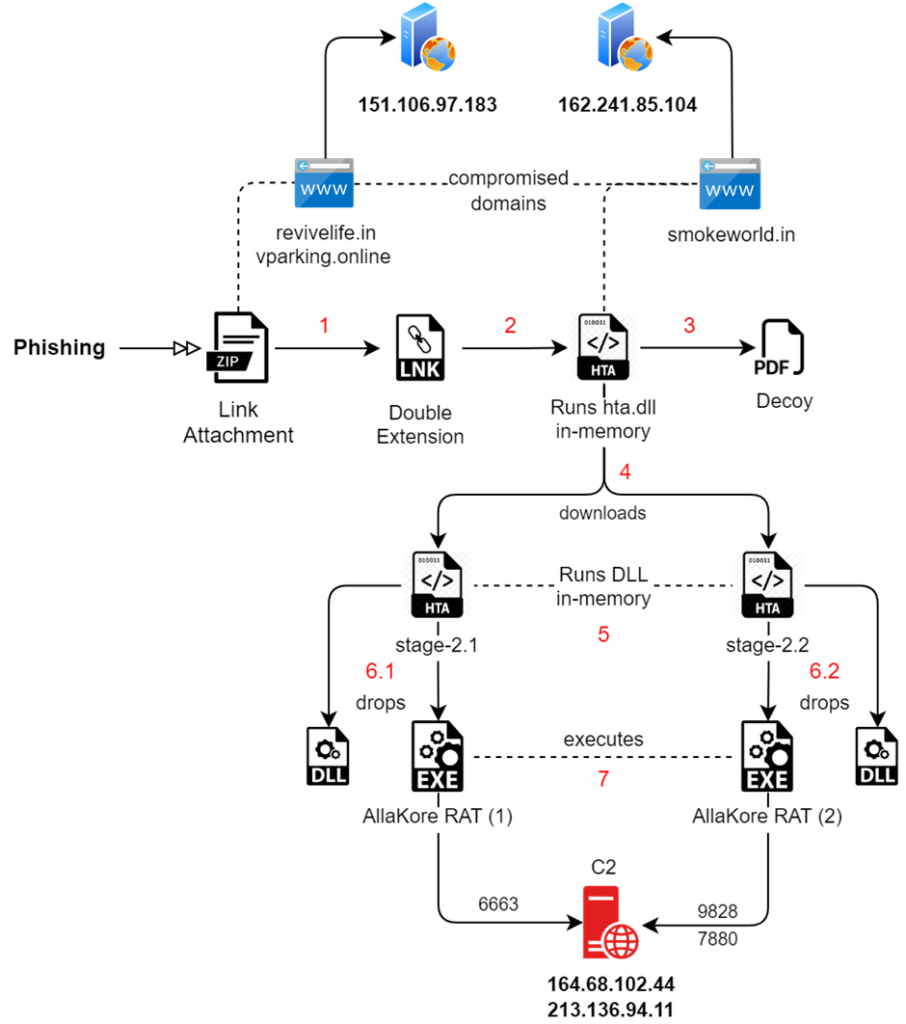
Cybersecurity experts at Seqrite Labs have reported a surge in cyberattacks against Indian government entities. These attacks have been attributed to Pakistani Advanced Persistent Threat (APT) groups, which have been intensifying their malicious activities. Attack Methods The recent campaigns uncovered by Seqrite Labs’ APT team reveal a sophisticated level of cyber warfare. Is Your Network Under Attack? - Read CISO’s Guide to Avoiding the Next Breach - Download Free Guide The Pa