Smart devices: using them safely in your home
<div>Many everyday items are now connected to the internet: we explain how to use them safely.</div>
<div>Many everyday items are now connected to the internet: we explain how to use them safely.</div>
<div>Risk appetites; what are they, what’s their purpose, how do organisations go about defining them?</div>
<div>Why I'm trying desperately to stop saying 'it depends' when it comes to simple cyber security questions...</div>
<div>The NCSC's Cloud Security Research Lead suggests some approaches to help you get confidence in cloud services.</div>
<div>An updated report from the NCSC explaining how UK law firms - of all sizes - can protect themselves from common cyber threats.</div>
<div>Recommended profiles to securely configure TLS for the most common versions and scenarios, with additional guidance for managing older versions.</div>
<div>How setting up 2SV can help protect your online accounts, even if your password is stolen.</div>
<div>Good cyber hygiene, which includes things like regularly changing passwords or applying software security patches, plays an outsized role in preventing America's adversaries from hacking into and crippling U.S. infrastructure systems.</div>
<div>Onur Aksoy, the CEO of a group of companies controlling multiple online storefronts, was sentenced to six and a half years in prison for selling $100 million worth of counterfeit Cisco network equipment to government, health, education, and military organizations worldwide. [...]</div>
<div>A challenge for DOD has been both competing with the private sector for talent, but also finding the best way to manage the talent it has and that it brings on are in the most appropriate jobs. </div>

Valuable information is buried in emails – from your clients, sensitive projects and legal matters. It is increasingly difficult to find, organize and see the full set of relevant information lawyers and other knowledge workers need to respond quickly and stay on top of their projects and cases. An ever-growing volume of email often leads to “content chaos” – burdened email servers, increased compliance risk, such as organization's retention policies, and the inability of employees to locate re
<div>Bitwarden, the creator of the popular open-source password manager, has just launched a new authenticator app called Bitwarden Authenticator, which is available for iOS and Android devices. [...]</div>
<div>CISA and the FBI urged software companies today to review their products and eliminate path traversal security vulnerabilities before shipping. [...]</div>
<div>Law enforcement shut down 12 phone fraud call centers in Albania, Bosnia and Herzegovina, Kosovo, and Lebanon, behind thousands of scam calls daily. [...]</div>

Brute force attacks are one of the most elementary cyber threats out there. Technically, anyone with a keyboard and some free time could launch one of them — just try a bunch of different username and password combinations on the website of your choice until you get blocked. Nick Biasini and I discussed some of the ways that organizations can defend against brute force attacks since detection usually doesn’t fall into the usual bucket (ex., there’s nothing an anti-virus program could detect run
<div>Microsoft has highlighted a novel attack dubbed "Dirty Stream," which could allow malicious Android apps to overwrite files in another application's home directory, potentially leading to arbitrary code execution and secrets theft. [...]</div>
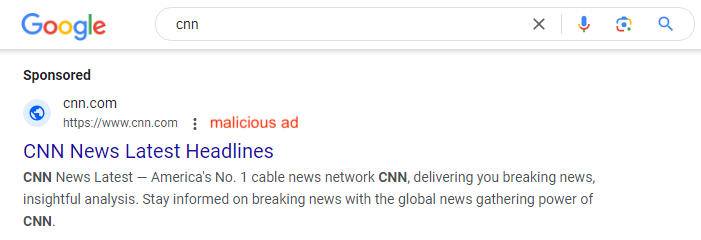
This blog post was written based on research carried out by Jérôme Segura. A campaign using sponsored search results is targeting home users and taking them to tech support scams. Sponsored search results are the ones that are listed at the top of search results and are labelled “Sponsored”. They’re often ads that are taken out by brands who want to get people to click through to their website. In the case of malicious sponsored ads, scammers tend to outbid the brands in order to be listed

Today’s businesses run on data. It fuels our decision-making, helps us enhance customer experiences, and drives innovation. However, all this data has a big downside: content sprawl. Consider a common scenario: a client sends you an important document as an email attachment. You save a copy to your company’s cloud storage platform, another to your desktop for quick reference, and then forward the email to the rest of your team—who do the same thing. Multiply this process daily across hundre
<div>Yaroslav Vasinskyi, a Ukrainian national, was sentenced to 13 years and seven months in prison and ordered to pay $16 million in restitution for his involvement in the REvil ransomware operation. [...]</div>
<div>Microsoft has confirmed that it won't provide an automated fix for a known issue causing 0x80070643 errors when installing recent Windows Recovery Environment (WinRE) updates. [...]</div>